What happens when you “crack”
An attacker tries many possible passwords.
Depending on the method (dictionary, pattern, brute force), variants are tested automatically.
Why is it taking so long?
Because the effort involved increases extremely quickly:
Each additional position multiplies the possible combinations.
Length has an immediate effect.
What makes a password truly strong?
Coincidence + length. “Complicated-looking” patterns are often surprisingly weak,
if they are predictable.
Use a unique, long password or passphrase for each service.
Length and randomness are more important than special characters or complicated patterns.
How StickSafe protects your data
- Data is stored in encrypted form (AES-256-GCM).
- Access only with master password.
- Emergency protection through PUK function.
- The data cannot be used without a password.
- Offline storage reduces unnecessary online attack surfaces.
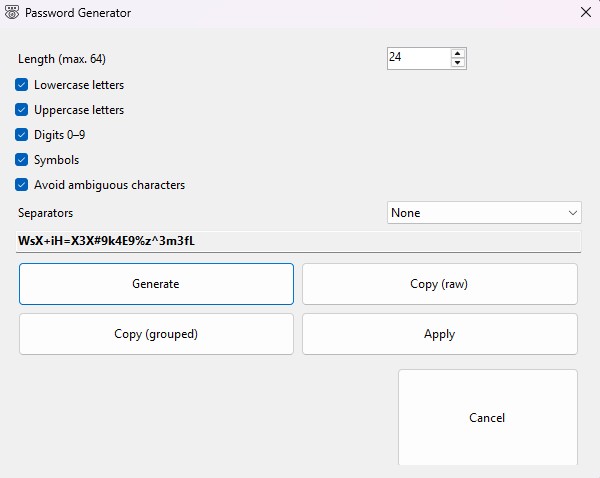
- Password generator helps to generate true randomness.
A random password with 24 characters is extremely difficult to guess because the number of possible combinations is enormous. It is crucial that it is truly random (no patterns, no words, no reuse).
Very long, random passwords or passphrases increase the effort required dramatically. In practice, this is not feasible for attackers if there are no vulnerabilities in the system.
Hardware, attack method, protection mechanisms used and, above all, the quality of the password. That is why time specifications on the internet are often misleading — the basic rule remains: length + randomness wins.
Rule of thumb: length beats everything
| Password type | Common mistake | recommendation |
| Short (8-12) characters, names, etc. | easy to guess / used too often | avoid |
| Medium (16+) | okay, if it really is by chance | good |
| Only (24+) | very strong by chance | very good |
| passphrase | strong, if not “proverbial” | very good |
The generator helps you create truly random passwords — this is the most significant security measure.